THE SMARTPHONE AGE
Chances are that your business has already done a great job shifting into the digital space. You’ve probably got a decent website, reasonably active social accounts, and a pretty good range of ways for customers, suppliers, and other stakeholders to contact you.
But it’s not enough. While you’ve been busy doing all the things necessary to build your brand, the world has changed around us.
The desktop PC is no longer the dominant piece of hardware –at home or in the office. We live in a mobile world now, We can work wherever there’s connectivity – meaning...
Hiring software developers for your team? Ask these 8 questions first
IT’S ALL ABOUT THE RELATIONSHIP
That’s because as much as choosing who will design the critical code that powers your business depends on their raw technical talent, that talent can’t be brought to bear if you’re not comfortable being around them.
In fact, it’s no exaggeration to suggest that the most successful software engineers are just as gifted with soft skills as they are with coding ability – and that these often-overlooked non-technical abilities are as crucial to the final outcome as anything else.
Because no matter how brilliant an individual or team of developers...
Italian ransomware attack highlights bad patch management
TARGETING THE WEAK
The newest attack impacted servers across Italy. At its peak, traffic was reduced to 26% of normal levels across the country. Servers in France, Finland, the United States, and Canada were also affected. The French cybersecurity agency, ANSSI, which issued the first alert on Friday, warned of continuing attacks against vulnerable servers in the days to come, and reiterated its guidance to administrators to patch their affected systems.
So, in case we’re keeping score, here’s where we’re at:
VMware identified a weakness in its products 2 years ago.
The...
Here’s why it takes so long to write great code
PICK ANY TWO OUT OF THREE
Anyone who has worked in the industry and knows what it takes to become a developer will appreciate how unfair this kind of reaction is. Because it fails to account for the years of education, training, and experience that fully qualified developers must go through.
It fails to recognize the massive investment developers must make to become top-performing professionals. Developers aren’t just born, and they don’t just materialize out of thin air. They need education (and lifelong learning), real in-the-trenches experience, and unbridled passion for writing...
Creative Disruption – why we should embrace change, not fear it
NO LONGER JUST NICE TO HAVE
All this uncertainty puts the usual year-end technology trend predictions in a somewhat darker context. And all of this got me thinking about the why of disruption.
See, every year, we read the trend reports – this year’s crop was chock full of predictions involving artificial intelligence, cybersecurity, BYOD, low code/no code development, quantum computing, and others – and then we set them aside and go back to work.
Sure, all of those hot trends sure sound incredibly cool – and make no mistake, nerds like us were all talking about them when we got...
Tech layoffs don’t mean that the sky is falling anytime soon
THE STORY BEHIND THE NUMBERS
Despite the frightening reality of an accelerating string of five-figure layoff notices, the sky isn’t falling. As is so often the case in tech, there’s context beyond the numbers. And in this case, the context of the broader jobs situation across the tech and tech-adjacent spaces tells us a bit of a different story.
Much of what we’re seeing is less dire-clouds-gathering-on-the-horizon than it is a structural realignment as we slowly emerge from the pandemic.
Indeed, as COVID first took hold in March 2020, many tech companies found...
FAA NOTAM outage should scare all of us into (finally) testing our DRPs
ONE BAD FILE
The Federal Aviation Administration has confirmed the event was triggered by an employee error that caused a corrupt file in the NOTAM system’s database. Worse, the backup system that would have been used to restore the database also contained the same corrupt file.
This should make IT practitioners cringe – I know I sure did. That’s because the presence of a corrupt backup strongly suggests the FAA’s disaster recovery plan (DRP) had likely not been tested in the leadup to this failure. Because the only way IT leaders would have known they had a problematic backup...
A new year means a new approach to cybersecurity
WATCH WHAT YOU CALL THEM, THOUGH
Let’s not call these resolutions, though. Because unlike our resolutions to eat better and get more steps in, we can’t afford to start ignoring cybersecurity before the first holiday credit card statement arrives in the mail.
Here’s a quick list of things you’ll want to zero in on as you tune up your organization’s cybersecurity strategy for 2023:
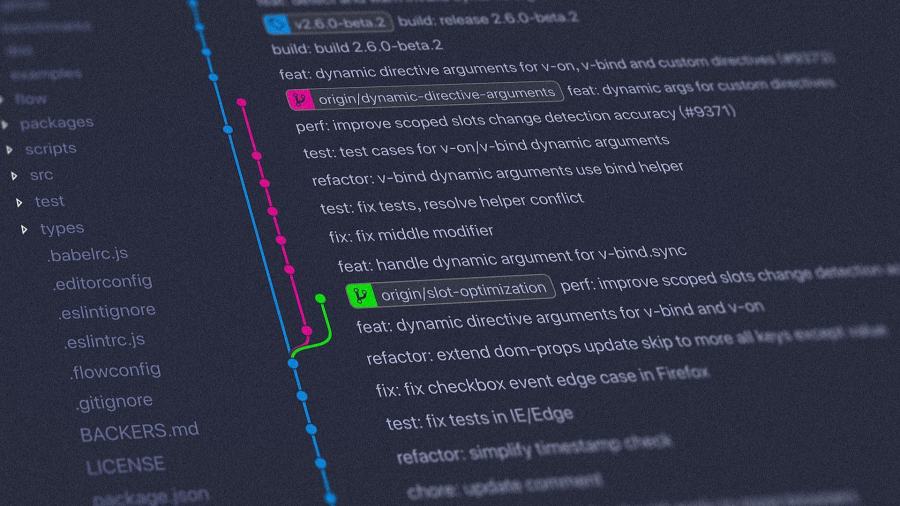
1 – UPDATE YOUR DEVICES AND SOFTWARE
You’re only as secure as your latest software update. We all know that outdated operating systems, apps, browsers, firmware, and any other form of code are...
Custom software or out of the box? The 5 reasons why custom could be the answer for your business
BUY OR BUILD?
One of the most important decisions any organization must make when deciding on a given software solution or project is whether they can buy it off the shelf or should be engaging developers to create custom software.
The decision is a complex one, and each approach has advantages and disadvantages that must be carefully weighed by a broad range of stakeholders. Back-end systems that support core business functions must have the features and capacity to accommodate current and future needs,
Similarly, end-user systems must incorporate the ideal set of features to...
Southwest Airlines meltdown: a reminder why software maintenance matters
IT WASN’T MOTHER NATURE’S FAULT
While the cancellation rate for most other major U.S. airlines – American, United, Delta, and JetBlue – ranged between 0 and 2% on the Tuesday before Christmas, Southwest had grounded 70% of its flights on Monday, and 60% on Tuesday. By Tuesday morning, Southwest’s schedule accounted for fully 2,522 of the 2,890 flight cancellations reported across the U.S.
The airline that has cultivated a scrappy, humorous brand since its founding in 1967 suddenly found itself tripped up by a crew scheduling system that couldn’t keep up.
The root...