EARLY AND BUGGY
Since ChatGPT was first made available for public consumption in late 2022, it has served as the poster child for the generative AI revolution. It has also become something of a proving ground for millions of AI newbies still trying to figure out how all of this applies to them.
But like any new technology, it comes with its own dark side. AI chatbots tend to “hallucinate”. Also known as going rogue, they can just as easily return outright lies the longer we interact with them. These imperfections are largely based on the fact that their training methods...
STEP Software celebrates 18 years – and looks to the future
RESET THE CLOCK
If we’re being really nitpicky – we’re developers, so we pretty much are – STEP Software’s history actually goes back 20 years, to 2003. That’s when our co-founder, Jim Freeman, developed an RSS reader and registered the overcow.com domain.
Why Overcow? Because it was the era of snappy, memorable, unconventional tech products and company names. And Jim wanted to pay homage to legendary Far Side cartoonist Gary Larson, who loved speaking about cows almost as much as he did. If Larson saw his other characters as being the bosses of the cows, then Jim thought...
Ongoing Twitter outages speak volumes about infrastructure’s importance
A GATHERING STORM
Whether it’s an API error, or simply a notification that you’ve exceeded your allowed number of followed accounts, it falls well short of a complete outage or a network-wide meltdown. To the typical end-user presented with these errors, Twitter is still largely operational, but it seems to be experiencing a series of annoying glitches here and there. Over time, the annoyance factor adds up.
None of this is enough to trigger a mass response from the platform’s 300 million users. Yet. But it is enough to highlight an unwelcome increase in the reports of intermittent...
TikTok bans are a long overdue wakeup call for mobile security
A GATHERING STORM
The Canadian move echoes similar moves in recent weeks by the U.S. government, the European Union, and at least half of all American states. It falls short of a full-on national ban, however such legislation has been proposed in the U.S. Nevertheless, this marks a serious foreign policy rebuke from Canada to China.
The growing global turbulence around TikTok reinforces the disparity between its populist perception as a non-threatening app, and accusations that it represents a major security threat on a personal, organizational, and national...
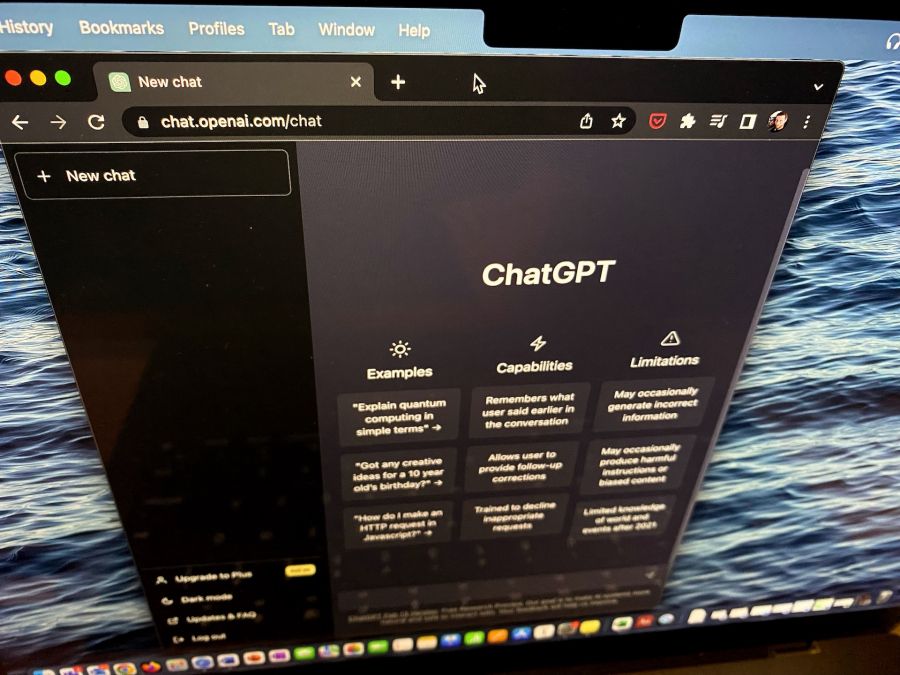
ChatGPT’s arrival reinforces the need to embrace – not ban – AI chatbots
WELCOME TO THE NEXT REVOLUTION
Artificial Intelligence (AI) has been one of those on-the-horizon technologies for what seems like forever. But public interest and engagement has been somewhat limited. That’s largely because it’s been accessible mostly to developers, researchers, and laboratories.
OpenAI’s decision to release ChatGPT to the public in November seems to have changed the game markedly. By opening up its consumer-friendly chatbot to everyday users, the organization, co-founded by Elon Musk, has sparked a global explosion of interest.
At the same time, all...
Building a mobile-friendly website? Do these 8 critical things first.
Note: This article continues our look at mobile-friendly websites, and why it has become essential for all businesses to have a mobile-first web presence. For guidance on making the business case within your own organization, check out our earlier article – Your business needs a mobile-friendly website. Here’s why.
THE WORLD LEADS WITH MOBILE
There is no longer any doubt that we live in a mobile world. Data from Statista confirms we’ve already passed something of a tipping point, and there’s no going back. According to this research firm, just over 59% of global...
Your business needs a mobile-friendly website. Here’s why.
THE SMARTPHONE AGE
Chances are that your business has already done a great job shifting into the digital space. You’ve probably got a decent website, reasonably active social accounts, and a pretty good range of ways for customers, suppliers, and other stakeholders to contact you.
But it’s not enough. While you’ve been busy doing all the things necessary to build your brand, the world has changed around us.
The desktop PC is no longer the dominant piece of hardware –at home or in the office. We live in a mobile world now, We can work wherever there’s connectivity – meaning...
Hiring software developers for your team? Ask these 8 questions first
IT’S ALL ABOUT THE RELATIONSHIP
That’s because as much as choosing who will design the critical code that powers your business depends on their raw technical talent, that talent can’t be brought to bear if you’re not comfortable being around them.
In fact, it’s no exaggeration to suggest that the most successful software engineers are just as gifted with soft skills as they are with coding ability – and that these often-overlooked non-technical abilities are as crucial to the final outcome as anything else.
Because no matter how brilliant an individual or team of developers...
Italian ransomware attack highlights bad patch management
TARGETING THE WEAK
The newest attack impacted servers across Italy. At its peak, traffic was reduced to 26% of normal levels across the country. Servers in France, Finland, the United States, and Canada were also affected. The French cybersecurity agency, ANSSI, which issued the first alert on Friday, warned of continuing attacks against vulnerable servers in the days to come, and reiterated its guidance to administrators to patch their affected systems.
So, in case we’re keeping score, here’s where we’re at:
VMware identified a weakness in its products 2 years ago.
The...
Here’s why it takes so long to write great code
PICK ANY TWO OUT OF THREE
Anyone who has worked in the industry and knows what it takes to become a developer will appreciate how unfair this kind of reaction is. Because it fails to account for the years of education, training, and experience that fully qualified developers must go through.
It fails to recognize the massive investment developers must make to become top-performing professionals. Developers aren’t just born, and they don’t just materialize out of thin air. They need education (and lifelong learning), real in-the-trenches experience, and unbridled passion for writing...