Tag: security
The Most Important Thing Nobody Wants to Write
Documenting software is the software developer equivalent to washing your windows.
Ask any developer how they feel about documentation, and you usually get a sigh, a grimace, or possibly a vague promise that they’ll “get to it later.” Unfortunately, just like windows, later means, harder, more work and in the worst-case scenario, a complete renovation. When “later” turns into “never”, organizations pay the price with onboarding delays, security gaps, and in some infamous cases — catastrophic project failures.
As most IT pros...
The 90-90 Aphorism of Great Software
Why 180% = 100%
Aphorism /ˈafəˌrizəm/ noun
“a short clever saying that is intended to express a general truth”
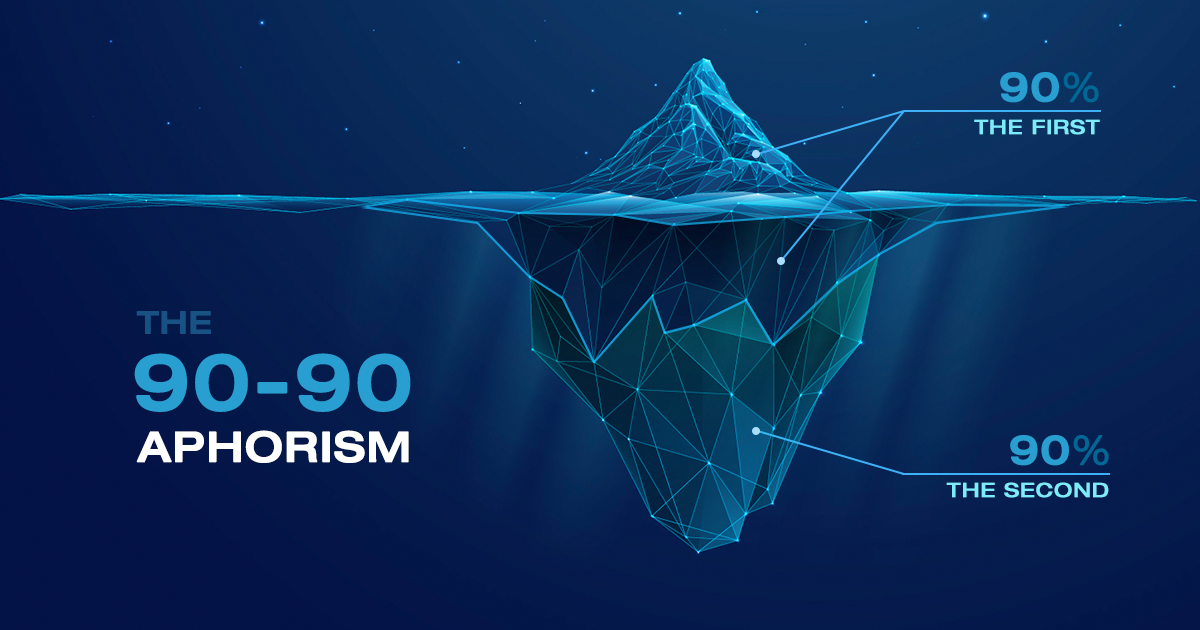
The 90-90 rule in software is the persistent illusion of “it’s almost done”. Tom Cargill of Bell Labs coined this aphorism back in 1985:
“The first 90% of the code accounts for the first 90% of the development time. The remaining 10% of the code accounts for the other 90% of the development time.”
You read that right, 180%. Welcome to software engineering.
180% = 100%, Really?
Yes, really!
If you’ve ever...
The True Cost of Technical Debt — And How IT Leaders Are Tackling It in 2025
In today’s digital-first economy, the pressure to innovate faster than the competition is unrelenting. But in that urgency, many organizations find, when looking back, that they cut corners; choosing short-term fixes over scalable, sustainable solutions. The result? Technical debt — a growing challenge that affects productivity, innovation, business continuity and even client relationships.
While some technical debt is strategic and manageable, much of it becomes a silent killer, slowly eroding an organization’s ability to evolve. In 2025, IT leaders are treating tech debt as a...
Stability at Speed, Innovation at Scale: Explore What We Can Do for You
At STEP Software we know that choosing a software development partner is a critical business decision. Whether you’re looking to modernize legacy systems, build a custom platform from the ground up, or scale your digital infrastructure, it’s essential to understand who you’re working with and what they bring to the table.
That’s why we’ve created an updated Capabilities Deck, now available for download directly from our website. It’s designed to give you a clear, concise overview of our technical expertise, industry experience, and the value we deliver on every...
Italian ransomware attack highlights bad patch management
TARGETING THE WEAK
The newest attack impacted servers across Italy. At its peak, traffic was reduced to 26% of normal levels across the country. Servers in France, Finland, the United States, and Canada were also affected. The French cybersecurity agency, ANSSI, which issued the first alert on Friday, warned of continuing attacks against vulnerable servers in the days to come, and reiterated its guidance to administrators to patch their affected systems.
So, in case we’re keeping score, here’s where we’re at:
VMware identified a weakness in its products 2 years ago.
The...
A new year means a new approach to cybersecurity
WATCH WHAT YOU CALL THEM, THOUGH
Let’s not call these resolutions, though. Because unlike our resolutions to eat better and get more steps in, we can’t afford to start ignoring cybersecurity before the first holiday credit card statement arrives in the mail.
Here’s a quick list of things you’ll want to zero in on as you tune up your organization’s cybersecurity strategy for 2023:
1 – UPDATE YOUR DEVICES AND SOFTWARE
You’re only as secure as your latest software update. We all know that outdated operating systems, apps, browsers, firmware, and any other form of code are...
Is Your Organization Prepared for a Ransomware Attack?
HOW THE ATTACKS WORK
Malicious software is used to deny access to data or systems until or unless the attacker’s ransom demands are met. Methods for delivering the malware payload vary, with the three of the most common being phishing emails, exploitation of application vulnerabilities, and delivery via remote desktop protocol (RDP). The use of phishing emails as an attack vector is currently on the rise.
Once successfully delivered, the malware propagates across data storage environments and/or vulnerable systems, rendering systems and data inaccessible. Attackers then demand...
Privacy Concerns: New Technology to Grade Meetings Through Surveillance of Attendees
HOW IT WORKS
Using sensors, cameras, and software algorithms, Microsoft’s “Meeting Insight Computing System” (MICS) will collect data on each meeting participant’s body language, expressions, and participation level. MICS will also track how much time attendees spend on activities that are not meeting-related, such as texting or reading email. For remote meeting participants, MICS factors in whether or not they activate their cameras. The system will also take environmental factors into consideration, including the temperature and level of noise in a meeting...
7 Common Myths About Hypertext Transfer Protocol Secure (HTTPS) You Shouldn’t Believe
1. IT DOESN’T AFFECT SEO
When analyzing the keywords and positions for which websites should rank, search engines place the greatest emphasis on content when calculating how websites should rank. However, HTTPS can still affect search engine optimization (SEO). If your website is powered by HTTPS, Google will favour it over your competitors’ HTTP websites. Google announced in 2014 that HTTPS websites would receive a slight boost in authority since they offer a safer and more secure experience for visitors.
While Bing doesn’t use it as a ranking factor, HTTPS may...
5 Ways an IT Provider can Save Your Business Money
1. CLOUD TECHNOLOGY
Technology is always changing, and purchasing the latest computer equipment can quickly devour your budget. However, a managed service provider will enable your business to use cloud technology, which gives your business access to the best tech available without any additional costs. Cloud technology also makes it more natural for employees to work together, whether they’re inside an office or in two completely different locations. An effective IT provider will also upload all of your information onto the cloud for the maximum protection against data loss.
...